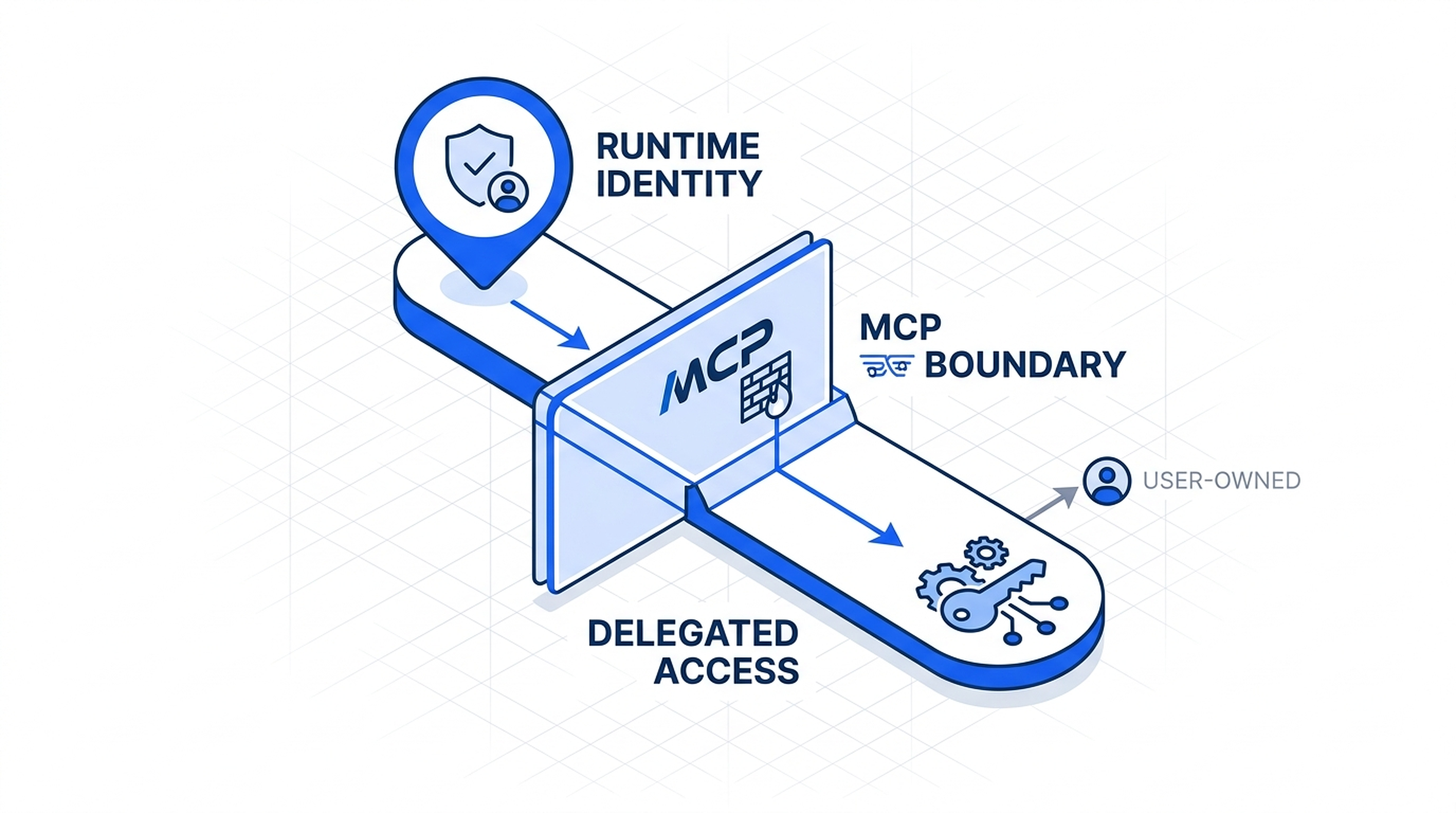
Why MCP Tool Access Does Not Replace Runtime Identity
MCP can narrow which tools an agent may call, but it does not replace runtime identity, delegated user access, or downstream system permissions.
Ideas
Thesis pieces, frameworks, build notes, and security briefs on the infrastructure, runtimes, and control layers underneath enterprise AI.
7 ideas Search by title, topic, or series.
Latest publication
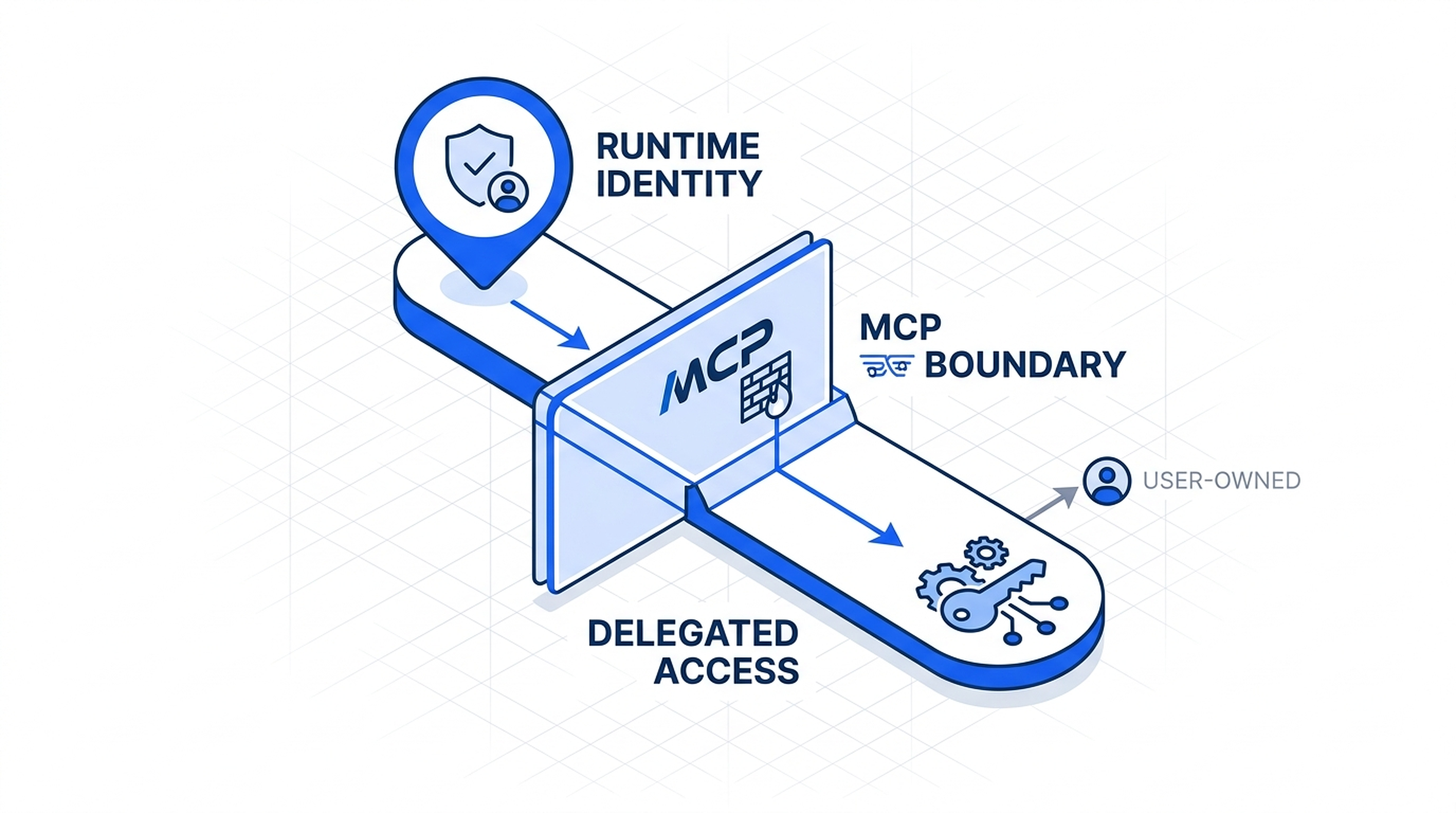
MCP can narrow which tools an agent may call, but it does not replace runtime identity, delegated user access, or downstream system permissions.
Archive

The real choice is not whether an agent has credentials. It is which identity pattern fits the ownership boundary around the action.
Most enterprise AI conversations start at the model layer. They should start several layers lower.
Triggers, validation, recovery, and auditability belong in the scaffold, not re-invented agent by agent.
The problem is not connector count. It is identity, scope, trust boundaries, and what the runtime is allowed to do.
Rules, ML signals, and LLM reasoning each have different jobs. Treating them as one layer creates brittle systems.
Autonomy, recovery, and access boundaries matter. Without them, it is automation wearing new language.
Try a different topic, format, or search term.